Phishing Definition Ict
Computers are very essential part of our daily lives and it plays an important roles in our lives. We would like to show you a description here but the site wont allow us.
Phishing And Pharming New Identity Theft Threats Presentation By Jason Guthrie Ppt Download
ICT policies usually include guidelines on.
Phishing definition ict. Customer who accessed the site and agreed to the clause and received ID and password and the qualification and authority are separately managed. The current definition used by the Computer Crime Research Center defines cybercrime as a crime committed online using a computer as a tool or as a. 13 Write a note on how IT can help an organization in gaining a competitive advantage on its operations. Estonia Case Concept of Cybercrime I felt the country was under attack by an invisible enemy. The Fortinet Security Fabric continuously assesses the risks and automatically adjusts to provide comprehensive real-time protection across the digital attack surface and cycle. Candidates have to score a minimum of 50 marks out of 100 in each paper.
Computer security cybersecurity or information technology security IT security is the protection of computer systems and networks from information disclosure theft of or damage to their hardware software or electronic data as well as from the disruption or misdirection of the services they provide. A token is something that is used to provide two-factor authentication. We launched this blog as part of our own learning process and we hope to engage the Digital for Development community as we find our way forward. Purchase and usage of hardware equipment and how to safely dispose them. AQA 8525 GCSE Computer Science. There is no negative marking.
Information and communication technologies désigne lensemble des technologies permettant de traiter des informations numériques et. DES is using an identical Continue reading. In this post we will focus on the different types of computer security such as application security network security internet security data security information security and end user security. Lacronyme NTIC ou TIC équivalent de langlais ICT. Application security is the types of cyber security which developing application by adding security features within. Article4 Definition of terms ① The definition of terms used in this agreement are as below.
An ICT policy is a set of guidelines that defines how an organization should use information technology and information systems responsibly. ICT is a single point of failure to Businesses. Candidates securing at least 45 marks in each subject with an aggregate of 50 marks in all subjects of examination in a single attempt will also be declared as having completed the examination. Person using the service who is not a member. Hacktivism Concept of Cybercrime. 14 Briefly describe one way how ICT can be applied in each of the following areas.
For first teaching in 2020. The field is becoming increasingly significant due to the continuously. CS 12 What is the difference between IT and ICT. We do not guarantee that it covers all of the relevant theory that is required for the examination. So the security of a computer is very essential because it protects our information and helps to prevent from viruses and malwareIn this post we will discuss on why is computer security important of our lives. Todays Enterprises Require a Security Fabric.
Modern ICT products and systems often integrate and rely on one or more third-party technologies and components such as software modules libraries or application programming interfaces. Last Updated on 6 months by Touhid. Choose two a token a DES key a private key a public key a TPM Explanation. Définition de NTIC nouvelles technologies de linformation et de la communication. ITE v70 IT Essentials Version 70 IT Essentials 70 Chapter 13 Exam Answers Which two items are used in asymmetric encryption. Powered by FortiOS the Fabric is the industrys highest-performing integrated cybersecurity mesh platform with the broadest open ecosystem for all.
Including online criminal activities such as phishing attacks botnets financial and banking fraud data fraud incidents and to promote basic multi. Types of Computer Security. The material on this site is not endorsed by the AQA examination board. The Digital for Development field has enormous potentialand plenty of room for learning. Information Communication Technology ICT policy.

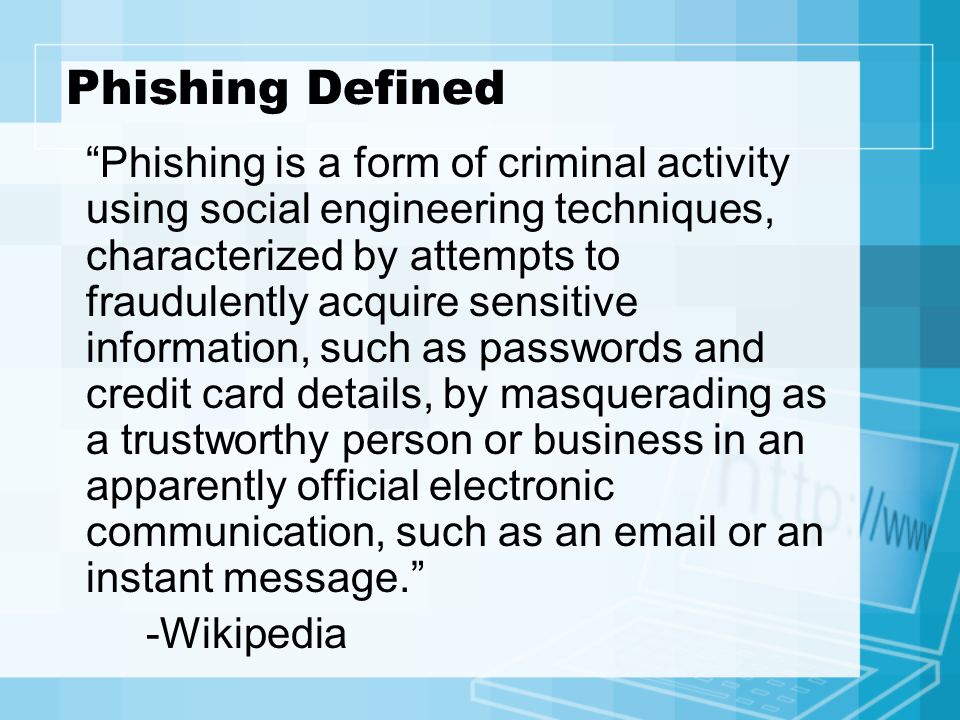
What Is Phishing Definition History Types Of Attacks
Frontiers Phishing Attacks A Recent Comprehensive Study And A New Anatomy Computer Science

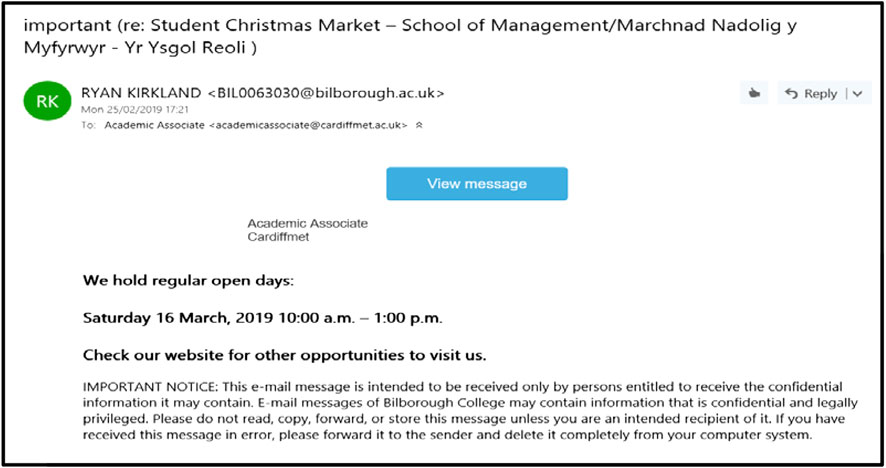
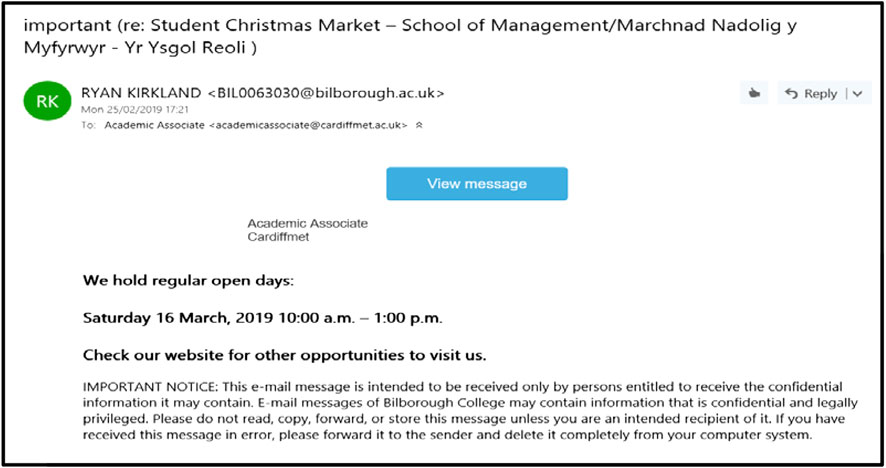
10 Steps Against An E Mail Phishing Attack Security Awareness App
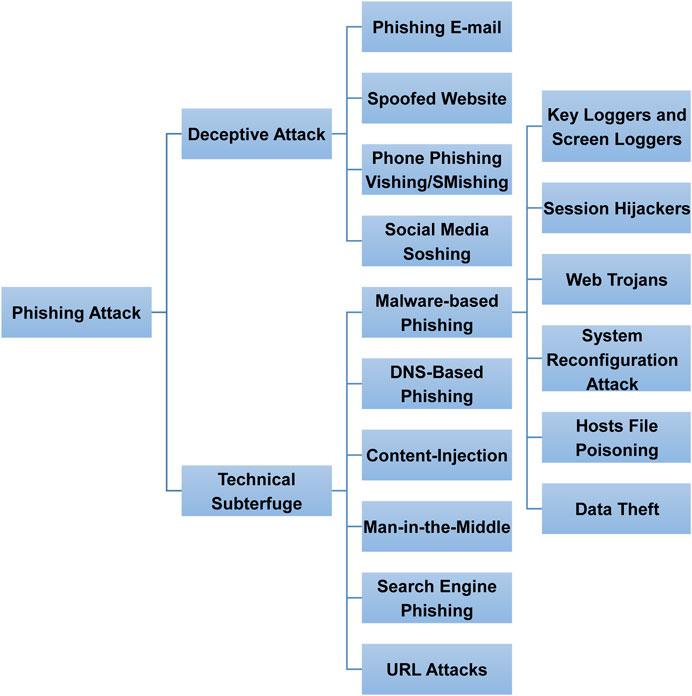
Frontiers Phishing Attacks A Recent Comprehensive Study And A New Anatomy Computer Science
What Is Phishing In Computer Technology It S A Number 1 Threat
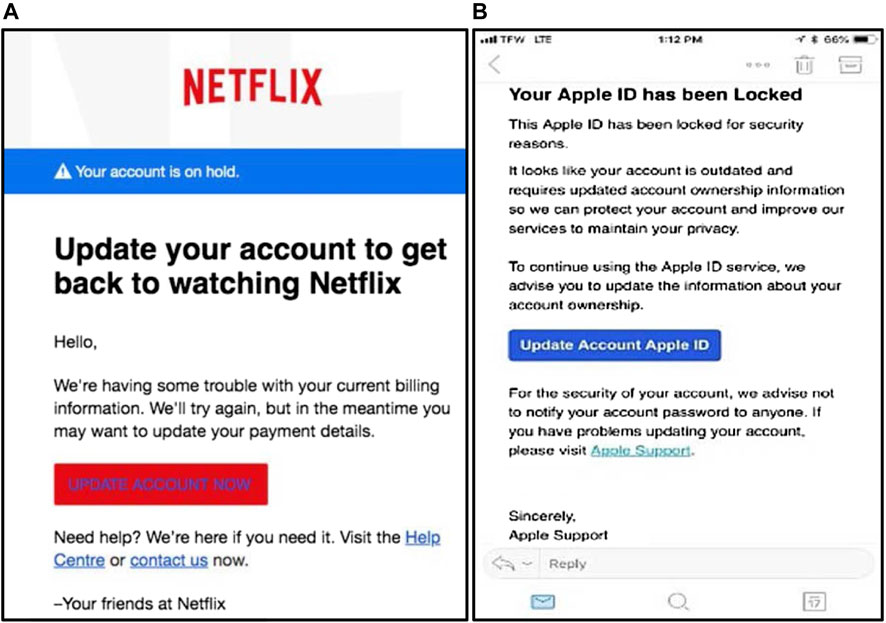
Frontiers Phishing Attacks A Recent Comprehensive Study And A New Anatomy Computer Science
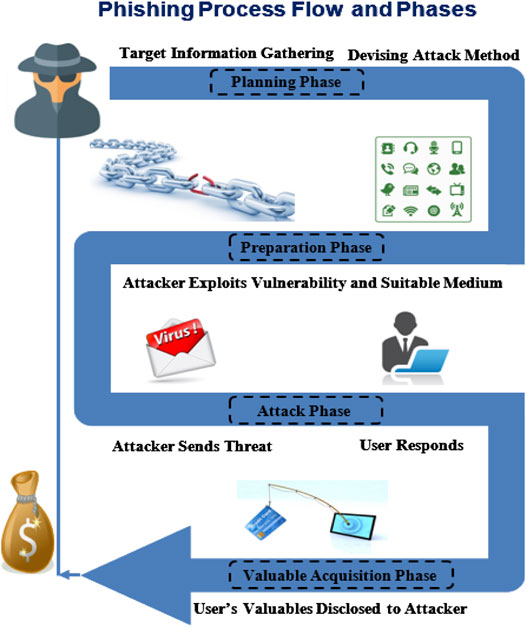
Frontiers Phishing Attacks A Recent Comprehensive Study And A New Anatomy Computer Science

Fake Facebook Phishing Attack Of Nepal Bangladesh Bank Fb Page

Phishing Computer Science Gcse Guru

Igcse Ict Internet Developments And Issues
What Is Phishing Definition From Techopedia

What Is A Phishing Attack Definition And Types Cisco

Posting Komentar untuk "Phishing Definition Ict"